Let's start with the main facts we know about the WADA hack, in chronological order:
1. Some point in time (August - September 2016), the WADA database has been hacked and exfiltrated
3. September 1st, the fancybear.net domain has been registered
Domain Name: FANCYBEAR.NET
...
Updated Date: 18-sep-2016
Creation Date: 01-sep-2016
5. The @FancyBears and @FancyBearsHT Twitter accounts have been created and started to tweet on 12th September, reaching out to journalists
6. 12th September, Western media started headlines "Russia hacked WADA"
The Threatconnect analysis
The only technical analysis on why Russia was behind the hack, can be read here: https://www.threatconnect.com/blog/fancy-bear-anti-doping-agency-phishing/After reading this, I was able to collect the following main points:
- It is Russia because Russian APT groups are capable of phishing
- It is Russia because the phishing site "wada-awa[.]org was registered and uses a name server from ITitch[.]com, a domain registrar that FANCY BEAR actors recently used"
- It is Russia because "Wada-arna[.]org and tas-cass[.]org were registered through and use name servers from Domains4bitcoins[.]com, a registrar that has also been associated with FANCY BEAR activity."
- It is Russia, because "The registration of these domains on August 3rd and 8th, 2016 are consistent with the timeline in which the WADA recommended banning all Russian athletes from the Olympic and Paralympic games."
- It is Russia, because "The use of 1&1 mail.com webmail addresses to register domains matches a TTP we previously identified for FANCY BEAR actors."
There is an interesting side-track in the article, the case of the @anpoland account. Let me deal with this at the end of this post.
My problem with the above points is that all five flag was publicly accessible to anyone as TTP's for Fancy Bear. And meanwhile, all five is weak evidence. Any script kittie in the world is capable of both hacking WADA and planting these false-flags.
A stronger than these weak pieces of evidence would be:
- Malware sharing same code attributed to Fancy Bear (where the code is not publicly available or circulating on hackforums)
- Private servers sharing the IP address with previous attacks attributed to Fancy Bear (where the server is not a hacked server or a proxy used by multiple parties)
- E-mail addresses used to register the domain attributed to Fancy Bear
- Many other things
The fancybear website
It is quite unfortunate that the analysis was not updated after the documents have been leaked. But let's just have a look at the fancybear . net website, shall we?Now the question is, if you are a Russian state-sponsored hacker group, and you are already accused of the hack itself, do you create a website with tons of bears on the website, and do you choose the same name (Fancy Bear) for your "Hack team" that is already used by Crowdstrike to refer to a Russian state-sponsored hacker group? Well, for me, it makes no sense. Now I can hear people screaming: "The Russians changed tactics to confuse us". Again, it makes no sense to change tactics on this, while keeping tactics on the "evidence" found by Threatconnect.
It makes sense that a Russian state-sponsored group creates a fake persona, names it Guccifer 2.0, pretends Guccifer 2.0 is from Romania, but in the end it turns out Guccifer 2.0 isn't a native Romanian speaker. That really makes sense.
What happens when someone creates this fancybear website for leaking the docs, and from the Twitter account reaches out to the media? Journalists check the website, they see it was done by Fancy Bear, they
Just imagine an expert in the USA or Canada writing in report for WADA:
"the hack was done by non-Russian, but state-sponsored actors, who planted a lot of false-flags to accuse the Russians and to destroy confidence in past and future leaks". Well, I am sure this is not a popular opinion, and whoever tries this, risks his career. Experts are human, subject to all kinds of bias.
The Guardian
The only other source I was able to find is from The Guardian, where not just one side (it was Russia) was represented in the article. It is quite unfortunate that both experts are from Russia - so people from USA will call them being not objective on the matter. But the fact that they are Russian experts does not mean they are not true ...https://www.theguardian.com/sport/2016/sep/15/fancy-bears-hackers--russia-wada-tues-leaks
Sergei Nikitin:
"We don't have this in the case of the DNC and Wada hacks, so it's not clear on what basis conclusions are being drawn that Russian hackers or special services were involved. It's done on the basis of the website design, which is absurd," he said, referring to the depiction of symbolically Russian animals, brown and white bears, on the "Fancy Bears' Hack Team" website.
I don't agree with the DNC part, but this is not the topic of conversation here.
Alexander Baranov:
"the hackers were most likely amateurs who published a "semi-finished product" rather than truly compromising information. "They could have done this more harshly and suddenly," he said. "If it was [state-sponsored] hackers, they would have dug deeper. Since it's enthusiasts, amateurs, they got what they got and went public with it.""
The @anpoland side-track
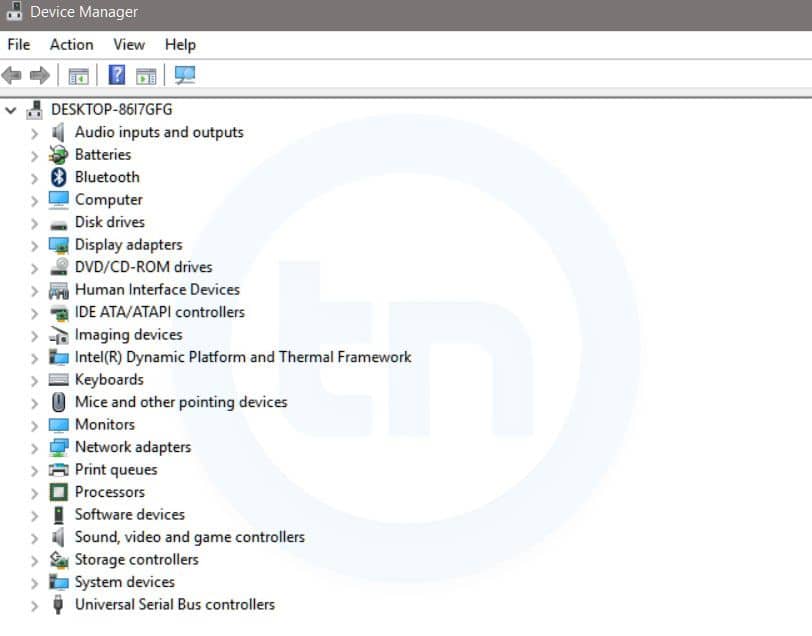
First please check the tas-cas.org hack https://www.youtube.com/watch?v=day5Aq0bHsA , I will be here when you finished it. This is a website for "Court of Arbitration for Sport's", and referring to the Threatconnect post, "CAS is the highest international tribunal that was established to settle disputes related to sport through arbitration. Starting in 2016, an anti-doping division of CAS began judging doping cases at the Olympic Games, replacing the IOC disciplinary commission." Now you can see why this attack is also discussed here.- My bet is that this machine was set-up for these @anpoland videos only. Whether google.ru is a false flag or it is real, hard to decide. It is interesting to see that there is no google search done via google.ru, it is used only once.
- The creator of the video can't double click. Is it because he has a malfunctioning mouse? Is it because he uses a virtualization console, which is near-perfect OPSEC to hide your real identity? My personal experience is that using virtualization consoles remotely (e.g. RDP) has very similar effects to what we can see on the video.
- The timeline of the Twitter account is quite strange, registered in 2010
- I agree with the Threatconnect analysis that this @anpoland account is probably a faketivist, and not an activist. But who is behind it, remains a mystery.
- Either the "activist" is using a whonix-like setup for remaining anonymous, or a TOR router (something like this), or does not care about privacy at all. Looking at the response times (SQLmap, web browser), I doubt this "activist" is behind anything related to TOR. Which makes no sense for an activist, who publishes his hack on Youtube. People are stupid for sure, but this does not add up. It makes sense that this was a server (paid by bitcoins or stolen credit cards or whatever) rather than a home computer.
The mysterious Korean characters in the HTML source
The Russians are denying it
Attribution
Let me sum up what we know:It makes sense that the WADA hack was done by Russia, because:
- Russia being almost banned from the Olympics due to doping scandal, it made sense to discredit WADA and US Olympians
- There are multiple(weak) pieces of evidence which point to Russia
- By instantly attributing the hack to the Russians, the story was more about to discredit Russia than discrediting WADA or US Olympians.
- In reality, there was no gain for Russia for disclosing the documents. Nothing happened, nothing changed, no discredit for WADA. Not a single case turned out to be illegal or unethical.
Altering the leaked documents makes no sense if it was Russia(see update at the end). Altering the leaked documents makes a lot of sense if it was not Russia. Because from now on, people can always state "these leaks cannot be trusted, so it is not true what is written there". It is quite cozy for any US organization, who has been hacked or will be hacked. If you are interested in the "Russians forging leaked documents" debate, I highly recommend to start with this The Intercept article- If the Korean characters were false flags planted by the Russians, why would they remove it? If it had been Russian characters, I would understand removing it.
- All evidence against Russia is weak, can be easily forged by even any script kittie.
Questions and answers
- Was Russia capable of doing this WADA hack? Yes.
- Was Russia hacking WADA? Maybe yes, maybe not.
- Was this leak done by a Russian state-sponsored hacker group? I highly doubt that.
- Is it possible to buy an attribution-dice where all six-side is Russia? No, it is sold-out.